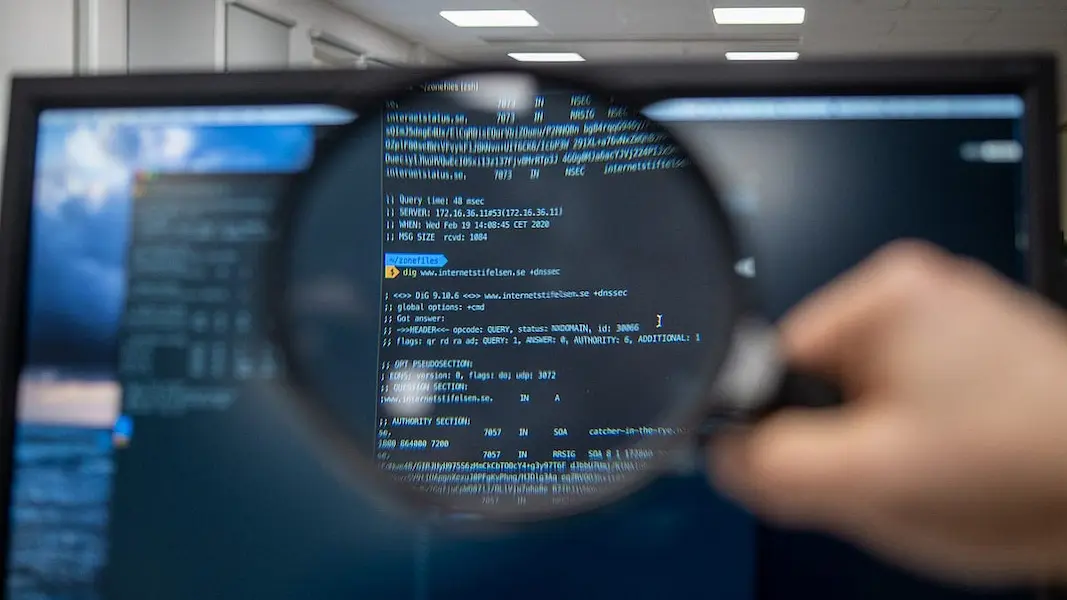
Grasping the tactics used by hackers is intriguing and crucial for constructing robust defensive strategies. By understanding their mindset, organizations can anticipate potential security breaches and take the necessary steps to reinforce their network’s vulnerabilities.
In recent years, cybersecurity incidents have become more frequent and severe. For example, the notable Fortinet hack highlighted the importance of network security and the clever tactics hackers use to penetrate defenses. It’s become evident that staying updated on the latest security breaches is invaluable for anticipating and thwarting potential attacks.
Key Takeaways:
- Acquire insights into hacker techniques to strengthen cybersecurity measures.
- Adopt a proactive approach to securing network infrastructure.
- Foster a culture of security awareness within the organization.
Table of Contents
Assessing Your Network: The Hacker’s First Move
The journey of bolstering your network begins with a critical assessment of your infrastructure’s current state, much like a hacker scopes out potential targets. Hackers meticulously scan systems for vulnerabilities using advanced tools and techniques. They exploit weak points such as outdated software, exposed services, and configuration errors. In a parallel strategy, organizations must adopt a routine of security assessments, meticulously examining their systems as an attacker would to identify vulnerabilities. Proactively patching these security gaps substantially reduces the risk of cyberattacks.
The Art of Social Engineering: Hackers’ Psychological Warfare
Hackers frequently exploit human predictability and psychology rather than hardware or software flaws. The social engineering involves manipulating individuals to divulge sensitive information or perform actions that compromise security. Attackers may pose as trusted entities, luring unsuspecting victims with deceptive emails, calls, or messages. The defense against this tactic is multi-faceted, starting with comprehensive staff training emphasizing social engineering risks. Companies should conduct mock drills and provide clear guidelines on handling suspicious requests. Proactive measures like these significantly bolster an organization’s human firewall against these psychological intrusions.
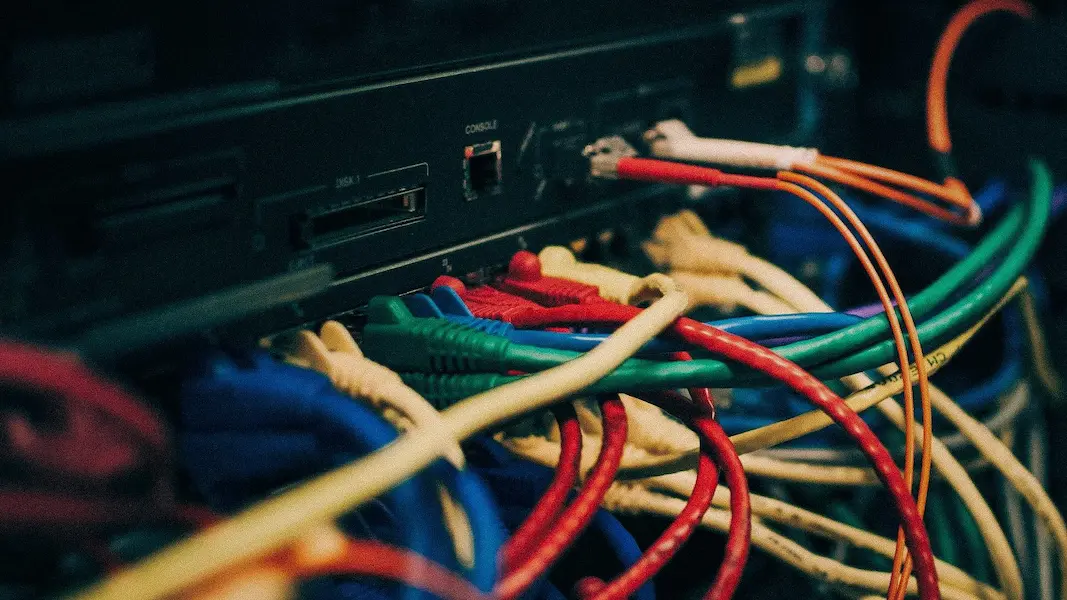
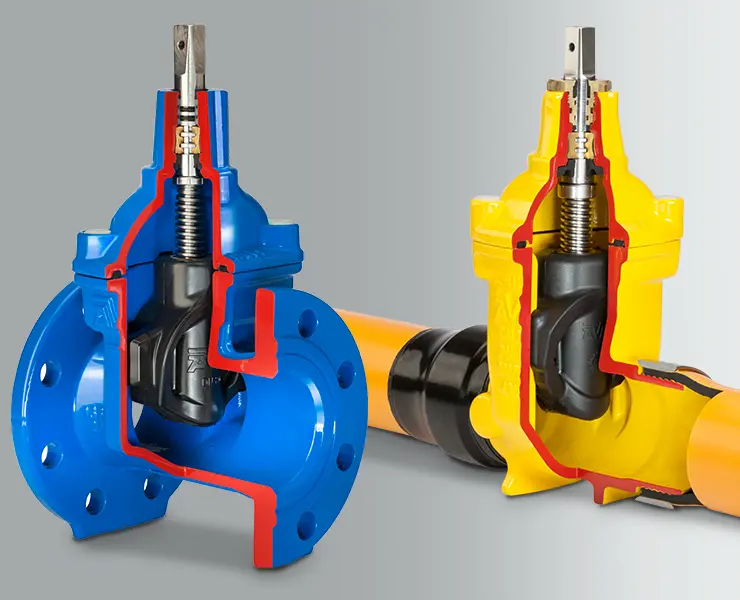
Securing Entry Points: Strengthen Your Network Perimeter
Your network’s perimeter is akin to the outer walls of a fortress, serving as the first line of defense against intruders. Hackers are consistently probing these perimeters for any sign of weakness. The secure management of these entry points involves not only the deployment of firewalls and routers with advanced threat detection capabilities but also the optimization of configurations for maximum protection. It’s essential to implement and consistently update layers of defense like intrusion detection and prevention systems. These systems act as vigilant sentinels, alerting network administrators to suspicious activities that could signify a breach attempt.
Encryption and Its Importance in Hacker Defense
Data encryption is a fundamental aspect of network security that converts sensitive information into a coded format understandable only to authorized entities with the decryption key. Effective encryption practices can prevent man-in-the-middle attacks, eavesdropping, and data tampering. Critically, it acts as a last line of defense, ensuring that even if data is intercepted or accessed unlawfully, it remains unintelligible and secure. Organizations must keep abreast of the latest encryption technologies and standards, implementing strong encryption protocols for data at rest and during transmission.
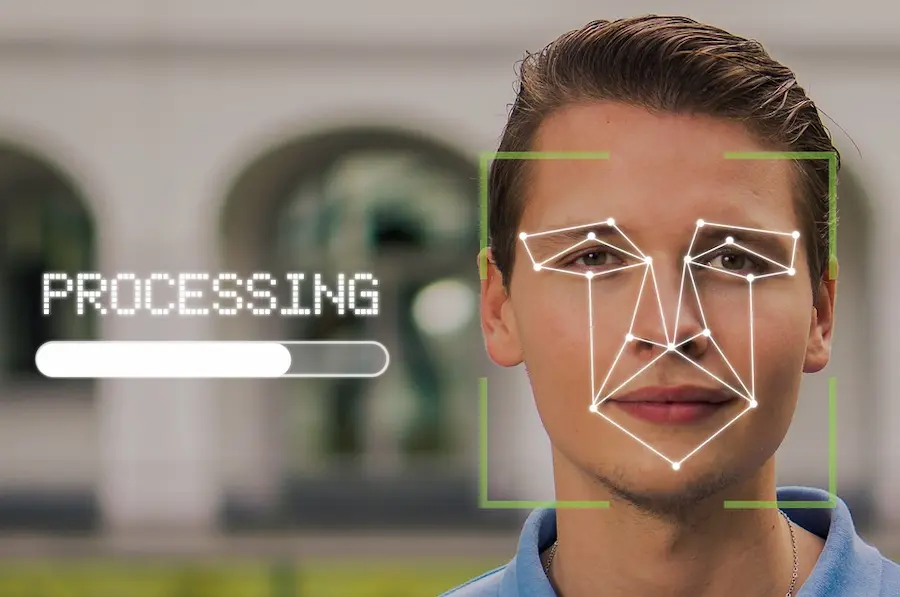
Detecting Anomalies: Behavioral Analysis to Prevent Breaches
Anomalies in network behavior often serve as harbingers of security breaches. State-of-the-art security systems now incorporate machine learning algorithms capable of discerning typical behaviors from anomalies. These systems provide early warnings of potential security incidents by analyzing patterns and flagging irregular activities. Integrating such advanced behavioral analysis into your security framework can dramatically increase your ability to preempt cyber attacks and respond to threats with swiftness and precision.
Phishing and Countermeasures: Training to Recognize Threats
Phishing attacks, wherein attackers masquerade as legitimate entities to solicit personal information, have remained a preferred method for breaching security. Training employees to recognize and react appropriately to phishing attempts is fundamental. This involves understanding the characteristics of phishing emails, such as urgent language and unverified sender addresses, and instituting strict protocols for verifying and reporting such incidents. Up-to-date training with evolving phishing methodologies is a strategic requirement for an informed and vigilant workforce.
Network Security Hygiene: Practices Every Employee Should Adopt
Robust network security extends beyond the IT department; it necessitates a company-wide commitment. Good network hygiene practices are crucial, encompassing strong password protocols, regular software updates, strictly controlled access permissions, and comprehensive data backup routines. Additionally, the widespread adoption of VPNs and secure wireless networks, especially for remote workers, is essential. When employees adhere to these practices, the network becomes a more formidable challenge for potential attackers.
The Future of Cyber Threats: Staying Ahead of the Curve
The cybersecurity landscape is constantly in flux, with new threats emerging as technology progresses. Organizations must be forward-thinking in their approach to security, not just reactive. This includes staying informed about emerging vulnerabilities, investing in ongoing employee education, and keeping pace with the advancement of cyber defense technologies. A proactive stance and continuous reassessment of security policies ensure preparedness for today’s and tomorrow’s cybersecurity challenges.
Implementing a ‘Hacker’s Mindset’: Continuous Ethical Hacking and Pen Testing
The maxim ‘to beat a hacker, think like a hacker’ underscores the value of ethical hacking. Organizations can expose and address security lapses from an attacker’s perspective by employing individuals skilled in penetration testing. Periodic ‘pen tests’ simulate real-world attack scenarios, offering invaluable insights into the effectiveness of current security measures and informing the necessary adjustments to counter the ever-evolving threats.
Building a Culture of Security: From Top Management to Every Employee
Creating an enduring security-conscious culture is a holistic commitment that involves active participation from all levels of an organization. When executives lead by example, prioritize cybersecurity, and allocate the necessary resources, they foster an environment where employees understand their role in protecting company assets. It is about engendering a mindset that views security not as a mere checklist item but as an integral part of the organizational fabric.












































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































0