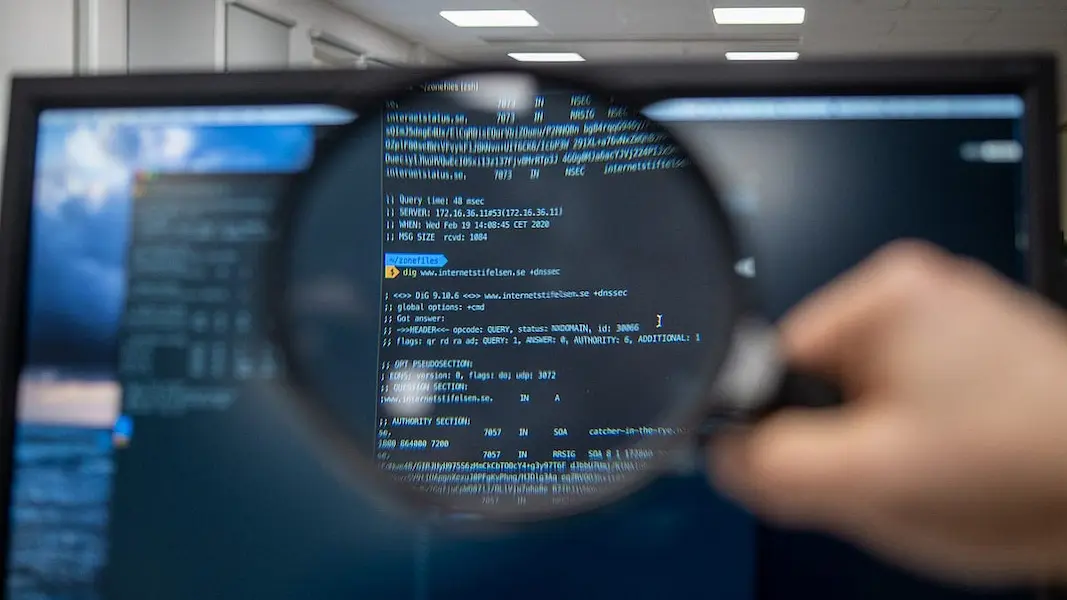
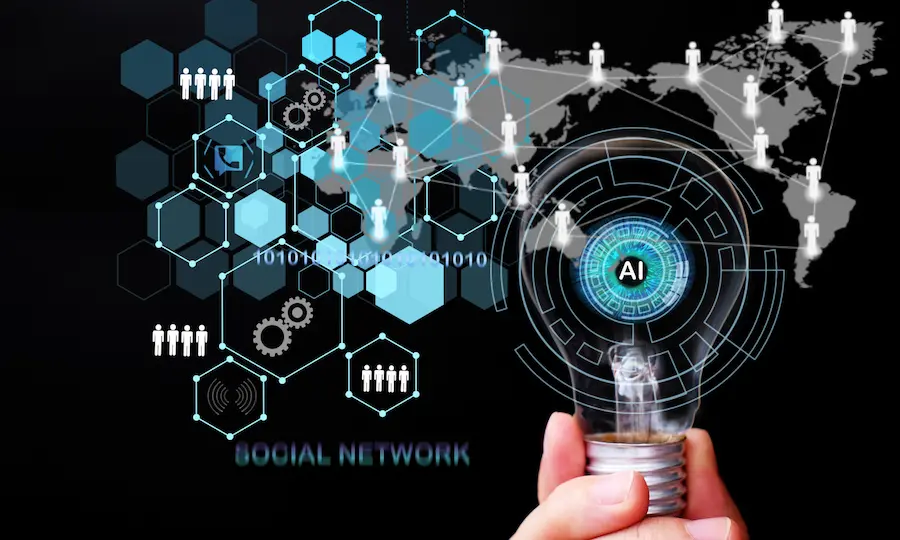
The world is dominated by digital technology. Be it desktop, laptop, tablet, or mobile; almost everyone is online at least once a day.
Anyone who goes online runs the danger of being a cyberattack victim, and these attacks may be disastrous for a company’s bottom line.
Businesses must consider cyber attacks as a big concern. New technology and increased cyber awareness have empowered cybercriminals with innovative ways to pull down our strongholds.
In this post, we will describe the most common types of cyberattacks. You can strengthen your security with this information and anticipate potential dangers ahead of time.
Table of Contents
1. SQL Injections
When an attacker injects malicious code into a functional server using Server Query Language (SQL), it forces the server to divulge protected information.
SQL injections can destroy tables, inspect user lists, and access administration databases. These strikes could have a disastrous impact on small to medium-sized enterprises.
Among other things, they can quickly cause distrust within their consumer base.
Generally, the most common method of carrying out this type of breach is entering malicious code into a search box that’s unprotected or comment section on a website.
One way to guard your system against SQL injections is to develop a comprehensive cyber security management plan.
Besides, regular network monitoring also helps to prevent SQL injections.
2. Malware
The term “malware” refers to malicious software. Simply put, any software meant to enter or harm a computer system without the owner’s knowledge is considered malware.
It is a broad category that includes threats such as ransomware, worms, trojan, and viruses.
In most cases, when you click a link or an attachment containing a virus, it is enough to activate the malware.
So before clicking on any link or attachment, you should consider its malicious potential. Avoid clicking links that do not come from legitimate sources.
Businesses should install the updated version of anti-malware software. A robust anti-virus and some degree of caution are often needed to avoid most malware threats.
3. Phishing
Cybercriminals use phishing attacks to deceive victims into providing sensitive information such as credit card details, passwords, intellectual property, etc.
An email purporting to be sent by a respectable bank, government authority, or some other trustworthy entity is a popular method of carrying out these cyberattacks.
Phishing is one of the most prevalent forms of cyber-attacks because they are comparatively simple to execute. The attacks can be avoided beforehand if you are a Certified Ethical Hacker or have the required expertise in this field.
Also, they result in successful breaches for the most part. Sometimes phishing attacks may not be limited to you.
If a hacker gains access to your contact list, email, or social media accounts, they could send phishing messages that appear to be from you to the people you know.
A phishing attack can be difficult to identify even for the most vigilant internet users because they have become increasingly sophisticated with time.
Here are a few measures to keep phishing attacks at a safe distance:
- Do not ignore updates: When you receive a slew of update notifications, it is easy to dismiss them. Avoid doing this. The most prevalent motivation for releasing security updates is to address the latest security flaws. If you skip updates, you put yourself at risk of falling prey to phishing scams.
- Change passwords frequently: The best way to keep a hacker from completely controlling your internet accounts is to change your passwords frequently. Ensure your password is a good mix of alphabets, numbers, and special characters.
- Download anti-phishing add-ons: Nowadays, most browsers allow you to install add-ons that look for warning signals of a fraudulent website or notify you about well-established phishing sites. Since they do not cost you a dime, make it a point to leverage these anti-phishing add-ons.
4. Denial Of Service
A denial of service (DoS) attack prevents your computer from responding to your requests. Your computer will stutter and freeze due to the onslaught of viruses. As a result of all the activity, your system will likely become unresponsive or malfunction.
There are a couple of reasons why these attacks are so common. The first reason is to avert any major business agreements from being finalized.
Broadly put, your company may be locked out of time-sensitive business negotiations and miss out on growth opportunities. This phenomenon is also known as a disrupted handshake.
The second most common use of DoS is to slow networks while other malicious attacks penetrate software.
As the network arranges and finishes processing the enormous amount of data, access to anti-virus software gets blocked, leaving your computer open to the most dangerous viruses.
A botnet is an infamous DoS that uses zombie systems to halt your network. Botnets use several “bots” to create fictitious locations worldwide, making it more difficult to track down the hacker.
Implementing multi-level security measures is best to protect your system from these cyberattacks.
Cloud-based services with pay-per-use requirements provide advanced and excellent defense against these threats.
5. Man-In-The-Middle
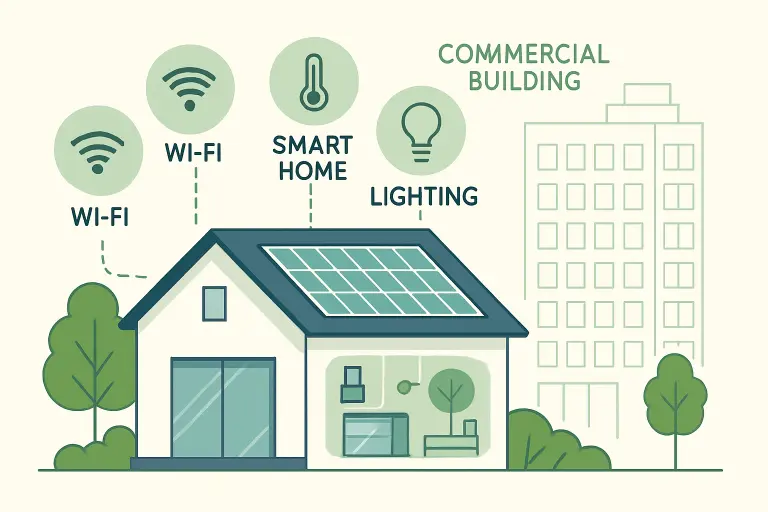
Man-in-the-middle (MitM) cyberattacks occur when malicious actors intercept or monitor personal communication between you and your employees or customers.
The most common purpose behind MitM attacks is to steal data and redirect it to another location. Due to the rise in the number of workers working from home after 2020, MitM poses a significant risk to companies’ data security.
Nowadays, a fair proportion of workers engage in official activities in public places. Coffee shops are examples of that.
If you are not careful, malicious actors can spy on you by installing fake Wi-Fi connections and easily commit a data reach without your knowledge.
With a VPN, you can defend yourself against MitM attacks. It will automatically encrypt all of your online activities.
Even though they could make your computer run a little slower, it would be at the expense of keeping your data safe.
Conclusion
When it comes to cyberattacks, many small firms believe they are too insignificant to be attacked. Sadly, this does not reflect the ground reality.
Cyberattacks are impacting all types of businesses regardless of their size or sector. Detailed knowledge about the different cyber security threats will ensure you stay on your toes and take prompt preventive measures.
Read also: 8 Reputable and Dependable Anti-Virus Applications












































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































0