Key Takeaways:
- Dive into the essence of application security testing and why it’s indispensable in modern software development.
- Recognize the varied and evolving strategies deployed in securing applications through testing.
- Explore the synergistic role of humans and technology in enhancing application security.
- Identify the significance of compliance and the influence of regulatory standards in security testing.
- Engage with future-centric discussions on the role of AI and ML in advancing application security testing practices.
Table of Contents:
- Introduction to Application Security Testing
- The Lifecycle of Secure Application Development
- Application Security Testing Techniques
- The Role of Penetration Testing in Application Security
- The Intersection of Compliance and Security Testing
- Evaluating Application Security Testing Tools
- Application Security Testing in the Cloud Environment
- Keeping Up With the Future of Application Security Testing
Table of Contents
Introduction to Application Security Testing
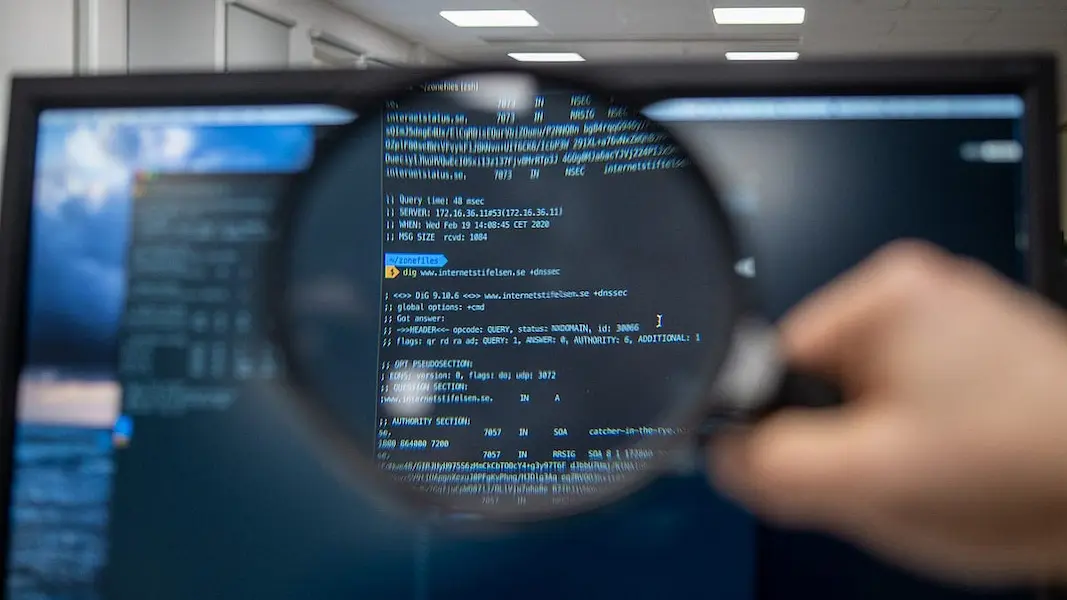
The importance of protecting software against the increasingly sophisticated landscape of cyber threats has led to the rise of application security testing. This proactive measure is essential for identifying and addressing vulnerabilities early in the application’s life, thus ensuring the safeguarding of sensitive data and maintaining user trust. Security testing employs techniques tailored to detect potential flaws, whether in code, design, or implementation, thereby mitigating risks before malicious actors can exploit them.
Modern businesses hinge their operations on the smooth functioning of software applications, making the security of these systems integral to their success. By detecting and resolving vulnerabilities early, application security testing not only preserves the integrity of software applications but also upholds the underlying business processes that rely on them. The ecosystem of digital products and services is as vast as it is intricate, bringing the critical need for robust application security protocols to the forefront.
The Lifecycle of Secure Application Development
Incorporating security testing into the software development lifecycle is much like weaving a solid thread through the fabric of the development process. Security testing should be an iterative cycle within each SDLC phase, beginning with the requirement analysis and stretching through to design, coding, and deployment. Companies that embed these practices stand to gain not just in terms of security but also efficiency, as potential issues can be identified and resolved without significant overhauls.
Adopting security testing as a core aspect of the software development process can reduce vulnerabilities that could be exploited post-deployment. Tools and methodologies that enable automated, continuous security assessments are becoming increasingly important. They allow for a more integrated and less intrusive approach to security, seamlessly blending it into the day-to-day workflows of development and operations teams and leading to more resilient software products.
Application Security Testing Techniques
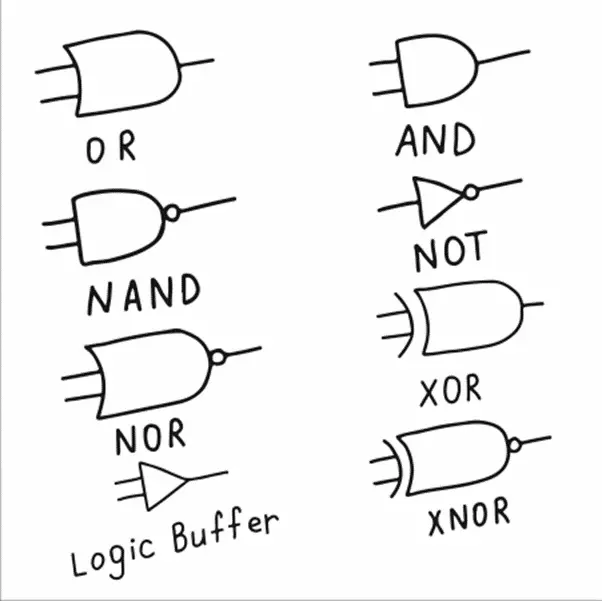
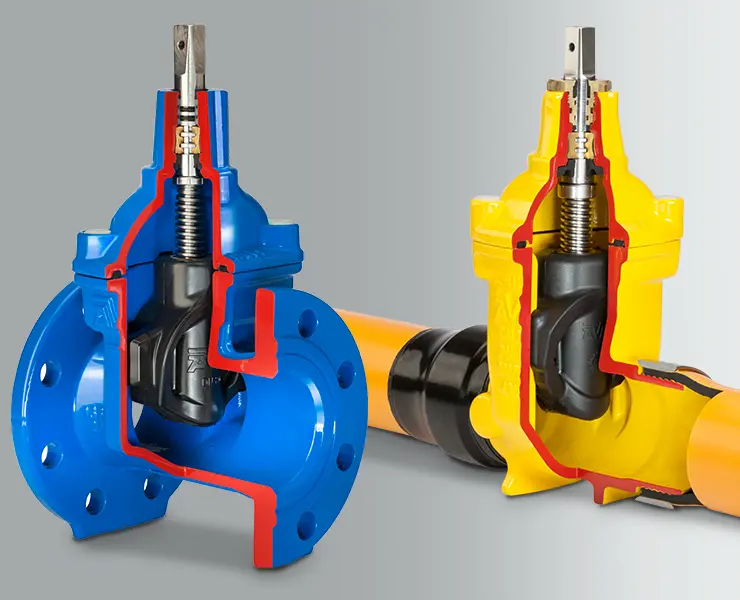
The arsenal of application security testing is diverse, providing multiple angles to assess and fortify applications. Static Application Security Testing (SAST) is akin to a detailed code review, where the source code is analyzed for potential vulnerabilities without executing the program. Dynamic Application Security Testing (DAST) takes an external viewpoint, assessing the application’s running state, operating much like an attacker to identify runtime flaws. Interactive Application Security Testing (IAST) represents the next evolution in testing techniques, combining the strengths of both SAST and DAST and offering real-time insights that help developers iron out security issues as they code.
The Role of Penetration Testing in Application Security
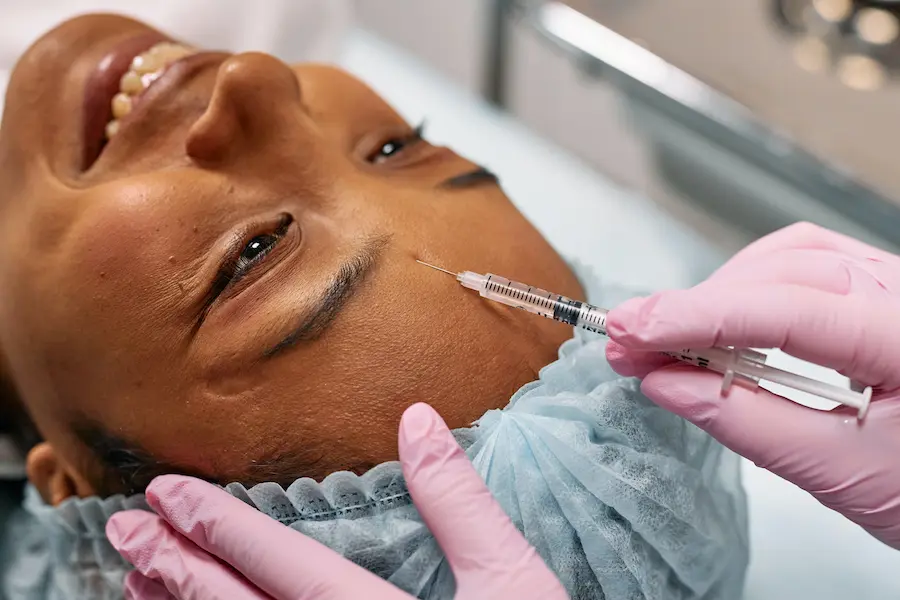
Automated tools are a boon for application security testing, yet they are not infallible. They may miss scenarios that an actual attacker could exploit. Penetration testing, conducted by skilled, ethical hackers, simulates a cyber-attack on the application to uncover exploitable vulnerabilities. This manual approach to testing brings a human perspective to identifying security weaknesses, offering insights into the practical implications of potential security breaches and helping organizations shape a robust security posture.
The Intersection of Compliance and Security Testing
Adhering to compliance standards is a multifaceted benefit of diligent security testing practice. Regulations are legal requirements and guidelines for best practices in application security. Organizations can avoid fines and gain the trust of partners and clients who respect data security and privacy by coordinating security testing efforts with these regulatory standards.
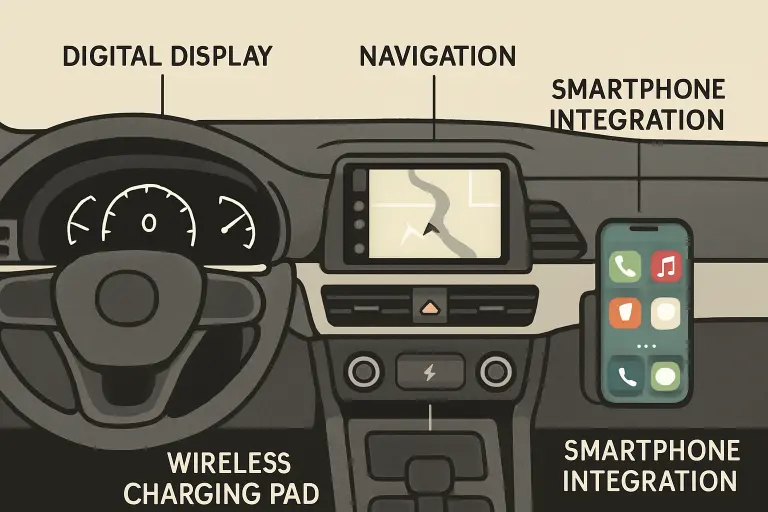
Evaluating Application Security Testing Tools
Choosing the right tools from a sea of available options demands a strategic approach. Modern applications are complex, flawless connection with current systems is necessary, and thorough coverage of a wide range of potential security risks is essential. All of these factors must be taken into account. Factors such as community support, customization possibilities, cost, and alignment with organizational requirements should inform the selection process between open-source and commercial solutions. Decision-makers must consider the overarching security objectives when evaluating the various tools.
Application Security Testing in the Cloud Environment
The adoption of cloud-based solutions has introduced novel challenges in security testing. Cloud-based services often involve a mixture of on-premises, public, and private cloud environments and dependencies on external services and APIs. This necessitates security testing approaches as flexible and dynamic as the environments they aim to protect. Protecting serverless architectures and containerized applications in the cloud calls for security practices that can pivot and scale alongside these modern development paradigms.
Keeping Up With the Future of Application Security Testing
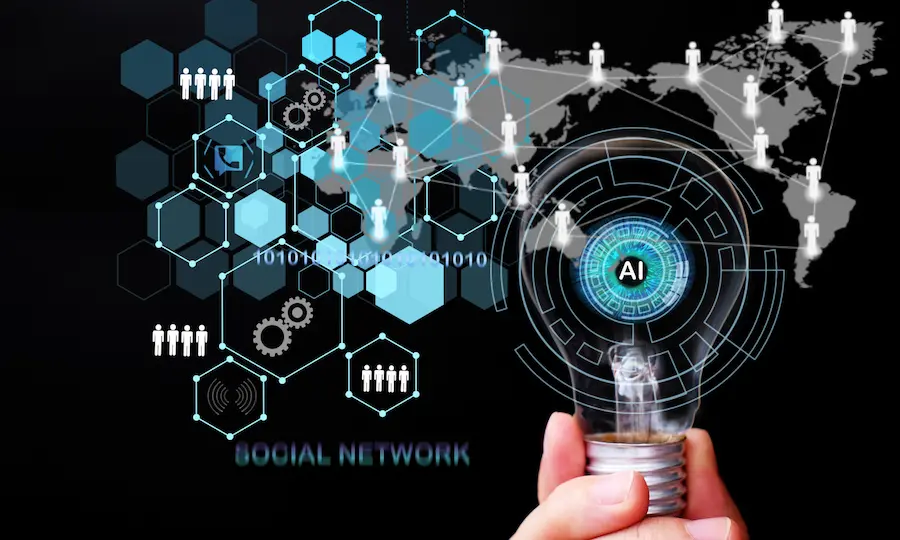
Rapid technological advancements, particularly in artificial intelligence and machine learning, shape the future of application security testing. These technologies promise to heighten the predictive capabilities of security testing, offering the ability to identify and respond to potential threats before they can cause harm. However, the reliance on technology must be balanced with continuous investments in developing human expertise to create a sustainable and resilient security testing ecosystem for the digital age.












































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































0