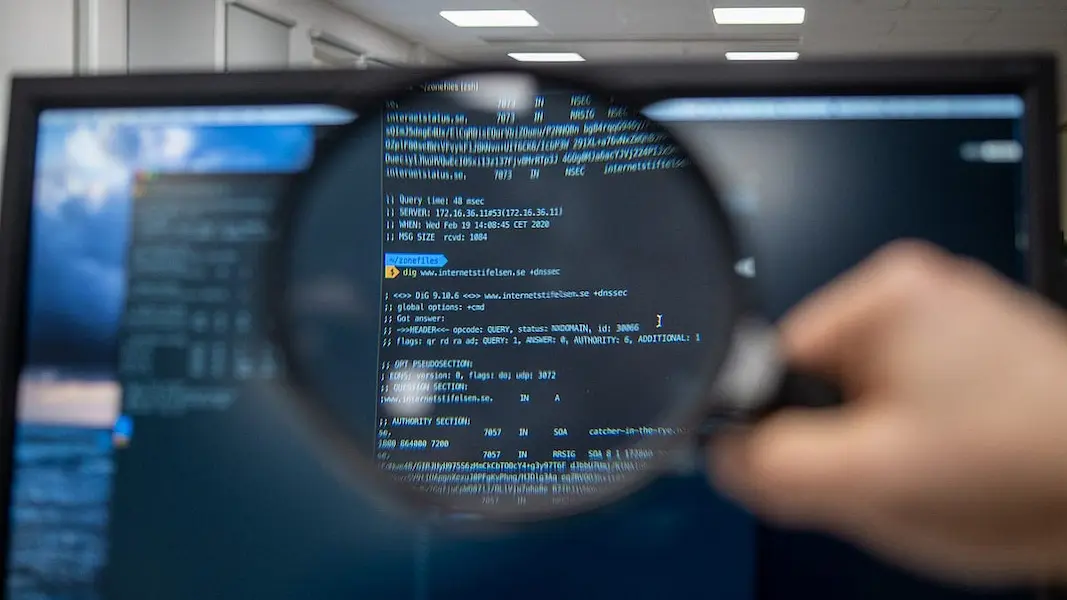
How can an organization address cybersecurity? Often the answer lies in implementing data governance, RBAC, and other best practices. However, other things can help your organization protect its data and systems. These practices may include physical control of devices and multi-factor authentication. If you’re interested in learning more about how to address cybersecurity in your organization, check out Eide Bailly. This article will teach you about cybersecurity and other important cybersecurity issues.
Table of Contents
Data governance
To protect data effectively, an organization must determine its data, where it is located, and who has access to it. Additionally, it must determine which security controls are necessary for its specific needs. This approach is essential for ensuring data is handled responsibly and lawfully. While this process can seem cumbersome, it will ultimately benefit everyone.
As the digital world becomes more interconnected, the concept of data governance must evolve to keep pace. In addition, the threat landscape, privacy regulations, and organizational boundaries constantly evolve. Therefore, organizations must adopt policies and procedures to protect their data. Data governance, in contrast, addresses these issues head-on. It helps organizations to avoid data breaches, improve core systems, and protect intellectual property. To do this, companies must develop policies that govern data and information and implement procedures that ensure its quality and integrity.
RBAC
Organizations need to map out the existing security situation to implement RBAC as a cybersecurity tool. While passwords protect most hardware and software, physical security is a key data protection component. Identifying the security gaps will allow you to adjust your security strategy accordingly. It would help if you also considered implementing RBAC in the different business areas and departments, including data, job functions, and technologies. Also, consider the potential impact of a cybersecurity event on your business.
By creating RBAC matrices, organizations can define the role-based access end users should have to sensitive data. For example, upper-level sales employees can create invoices, while lower-level employees can only read them. The same process can be used for data access. In addition, RBAC matrices can be created independently of technical implementation. The goal is to capture an organization’s organizational structure and make the necessary data access requirements concrete.
Multi-factor authentication
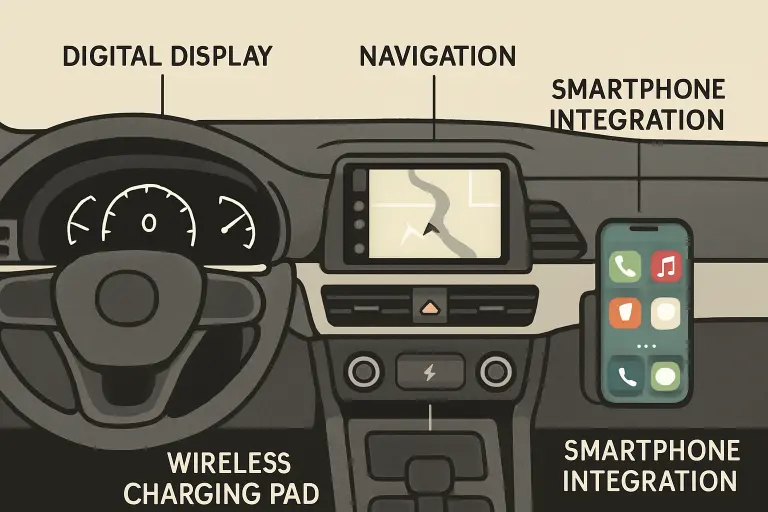
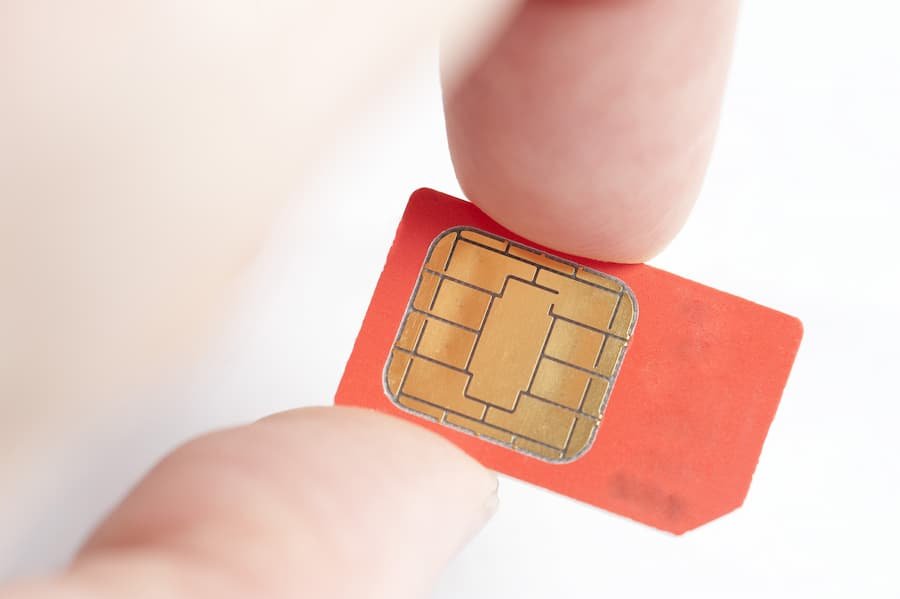
One of the best ways to protect against cyber threats is to implement multi-factor authentication (MFA). By using two separate methods to verify an individual’s identity, such as a password and a mobile phone, a company can prevent bad actors from gaining access to an account. MFA can be implemented on any device, including mobile phones, laptops, and desktops. Many devices support this technology, and one-click apps can be used to add MFA verification.
While many organizations use multi-factor authentication to secure their networks, not all do. Some organizations only implement it in suspicious circumstances. Regardless, the benefit is clear: it reduces the risk of unauthorized access to the system. While this can reduce the risk of duplicate passwords, organizations should be cautious about allowing unauthorized users to gain access to sensitive information. For example, multi-factor authentication limits the number of users accessing company resources. Only the individuals listed in the system can access the account by requiring a unique mobile device or email address.
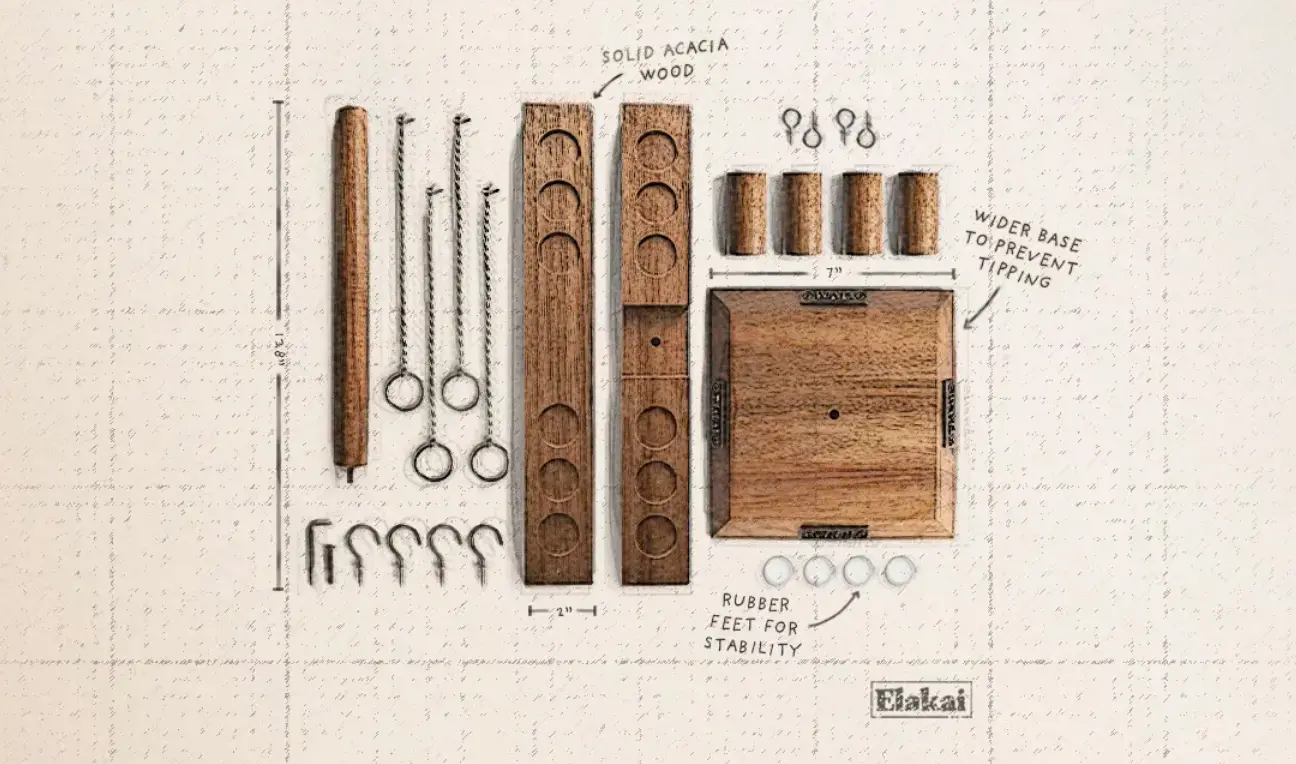
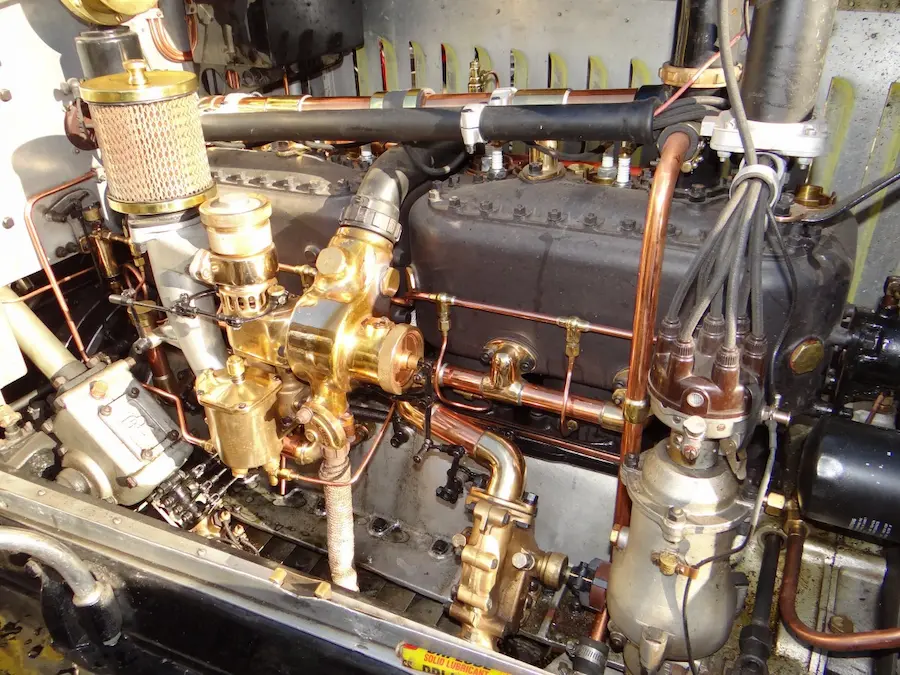
Physical control of your devices
The physical control of your devices for cybersecurity in organizations is an important component of a company’s overall cybersecurity strategy. While some physical security controls are inexpensive, others require more investment of time and money. Either way, they all contribute to the overall physical security posture of an organization and protect the assets and employees of that company.
As a cybersecurity specialist, I believe that physical control of your devices is essential to organization security. If you’re concerned about data breaches and are working with medical devices, you must take extra precautions to protect your sensitive data. Unattended devices are prime targets for cybercriminals. To combat this, ensure your employees always keep their mobile devices on them. Use security cables to secure laptops and other valuables when you’re not using them.
Training employees
Identifying and preventing cybercrime is a vital element of any cybersecurity training program. Unfortunately, cybercrime is on the rise, especially in light of the COVID-19 virus, increased remote working, and more sophisticated detection methods. Therefore, organizations should provide regular cybersecurity training and integrate opportunities to reinforce safe online behaviors into the daily work schedule. Cybersecurity training should also consider the evolving threat landscape and the needs of individuals.
Employee email habits are a common source of cybersecurity risks. Whether phishing sites are used to steal information or access social accounts, employees’ email habits leave the company wide open to cyberattacks. Cybersecurity training should address the best practices of email habits and provide guidelines for safe browsing. In addition, employees should be rewarded for adopting cybersecurity policies and enforcing them. Training employees should also cover how to protect company data through proper use of company devices and email.
Read also: Why Business Transcription is Essential for the Growth of Your Startup?












































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































0