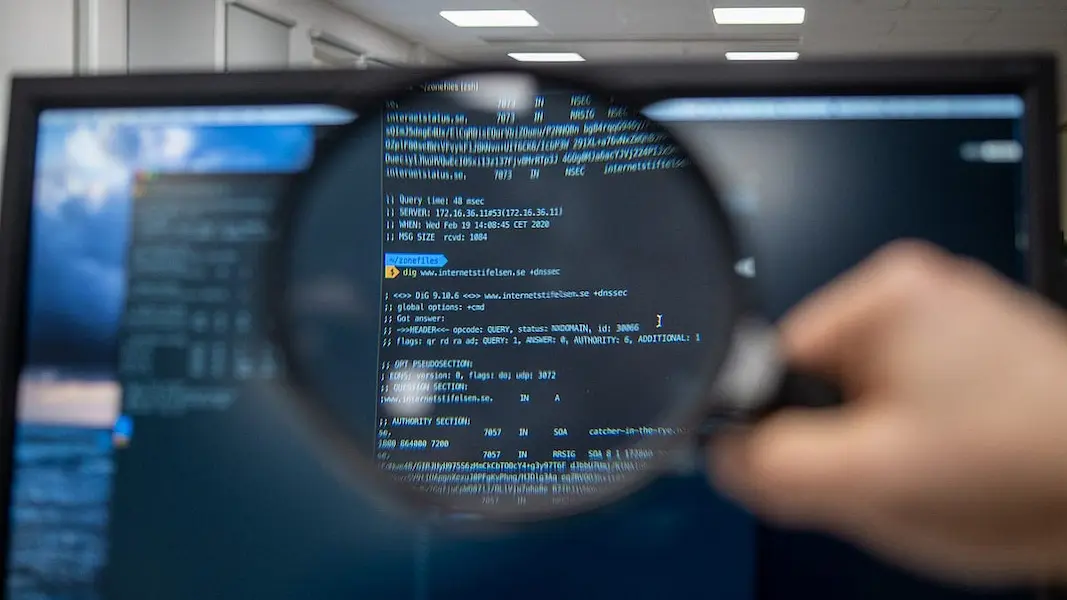
VPN stands for a virtual private network and it has been a buzzword in the cybersecurity sector for a while now. Whether you use it in a personal or professional context, your online privacy can be increased with the use of a VPN. You can browse the internet safely by hiding your identity. Thankfully, setting one up doesn’t require you to be an expert in cybersecurity.
With so many different VPN types that are on the market right now, it might seem challenging for you to figure out how to set up each one of them. You can take a look at our quick guide to learn how to set up the VPN your company needs.
Table of Contents
Various VPN Protocols And How To Set Them Up
VPN protocols provide the precise path that data takes across a connection. Based on the advantages and desired situation, these protocols have a variety of specifications.
PPTP VPN
PPTP (point-to-point tunneling protocol) is one of the first VPN protocols still in use. Microsoft created PPTP in the 1990s; it was included in Windows 95 and was made especially for dial-up connections. Although it isn’t the most modern VPN protocol out there, it is still used for secure web connections.
A VPN connection is established for a remote device using a PPTP VPN server. You must activate the PPTP VPN server on your router and set up the PPTP connection on your remote device in order to use the VPN services.
L2TP/IPSec VPN
A major drawback of L2TP (layer 2 tunnel protocol) is that it doesn’t provide any encryption. It is used in conjunction with IPsec encryption because of this. You can secure your data using either L2TP or IPsec, two separate protocols.
Since L2TP is a tunneling protocol, it establishes a unique connection for data transmission. All communication flowing on an IP network is protected against eavesdropping and packet manipulation by other networks thanks to IPsec’s network layer encryption. This creates a secure connection.
OpenVPN
A secure tunnel between two places in a network is made possible by the open source connection protocol known as OpenVPN. In plain English, this implies that many VPNs employ it as a trusted technology to ensure that any data transferred over the internet is encrypted and secure.
To set up OpenVPN, you just need to go to your VPN provider’s application or software and select OpenVPN from the settings. This is because most VPN providers have OpenVPN as a service in their systems. You can be sure that your data is secure with an OpenVPN protocol.
SSTP VPN
SSTP (secure socket tunneling protocol) is commonly used in VPNs. Microsoft created the technology to take the place of Windows’ less secure PPTP and L2TP/IPSec protocols. The majority of native VPN connections in Windows utilize SSTP, although the protocol used depends on the VPN provider and how simple it is for users and administrators to set it up.
You might be able to utilize Windows SSTP if you are subscribed to a VPN service. If SSTP is a choice for you in your VPN vendor, you can turn onn SSTP from settings much like OpenVPN.
IKEv2 VPN
Over the past few years, IKEv2 VPN has grown in popularity, especially among mobile users. Given how effective and secure the protocol is, it’s not difficult to understand why. It ensures security by first requiring the client and server to authenticate each other, and then deciding on the appropriate encryption techniques.
OpenVPN Vs IKEv2
Out of all these VPN protocols, OpenVPN vs IKEv2 is one of the most commonly compared ones. IKEv2 and OpenVPN both offer comparable degrees of security. The biggest distinction is that IKEv2 is not open-source, whereas OpenVPN is. They function differently because OpenVPN protects data in transit rather than at the IP level.
In comparison to IKEv2, OpenVPN is a little bit more involved, but it has global recognition and is supported by many VPN vendors. IKEv2 should be faster than OpenVPN due to this reason because it uses less CPU power. However, OpenVPN is less likely to be banned by firewalls.
Final Words
It’s not difficult to use a VPN. All you have to do is download the program, pick a location, and click the connect button. However, if we go a little further, there is more to play with: VPN protocols. They set up VPN tunnels so that data can be exchanged securely.
Your use case should guide your choice of VPN protocol. Not all VPN vendors will support all VPN protocols. Based on your operating system and other restrictions, you should realistically choose the best solution. OpenVPN and IKEv2 are two of the current VPN protocols that are the most dependable.
As always, one you know what you’ll use the VPN protocol for, choosing the best possible solution should not be difficult.












































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































































0